Network Security Video Production for Enterprise Technical Sales
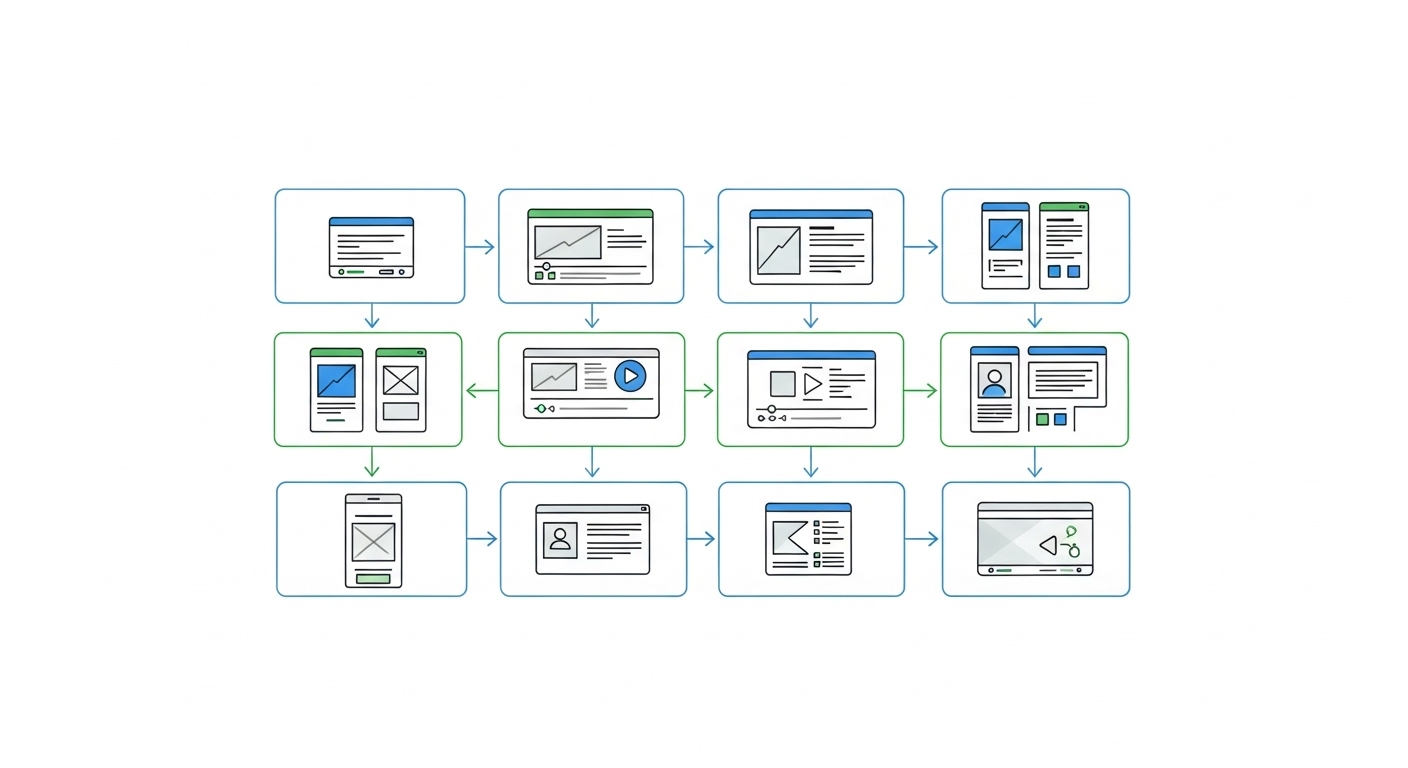
Security software and hardware vendors face elongated sales cycles due to the complexity of modern threat landscapes. Advids provides technical video creation that maps complex infrastructure to business outcomes, ensuring your technical value proposition is understood by both CISOs and procurement teams.
Over 42 videos for Network Security Companies